MFA 101
Those of you who own a small to a mid-sized business may be wondering what you can do to bring about better IT security. That’s a question you may ponder every day in your business as cybercrime continues to increase. One of the best security methods is the use of a multi-factor authentication process or MFA.
Recently, Jon Fausz (Chief Operating Officer at 4BIS) explained what an MFA is and why you need to use it to protect your business going forward.
Defining What MFA Is
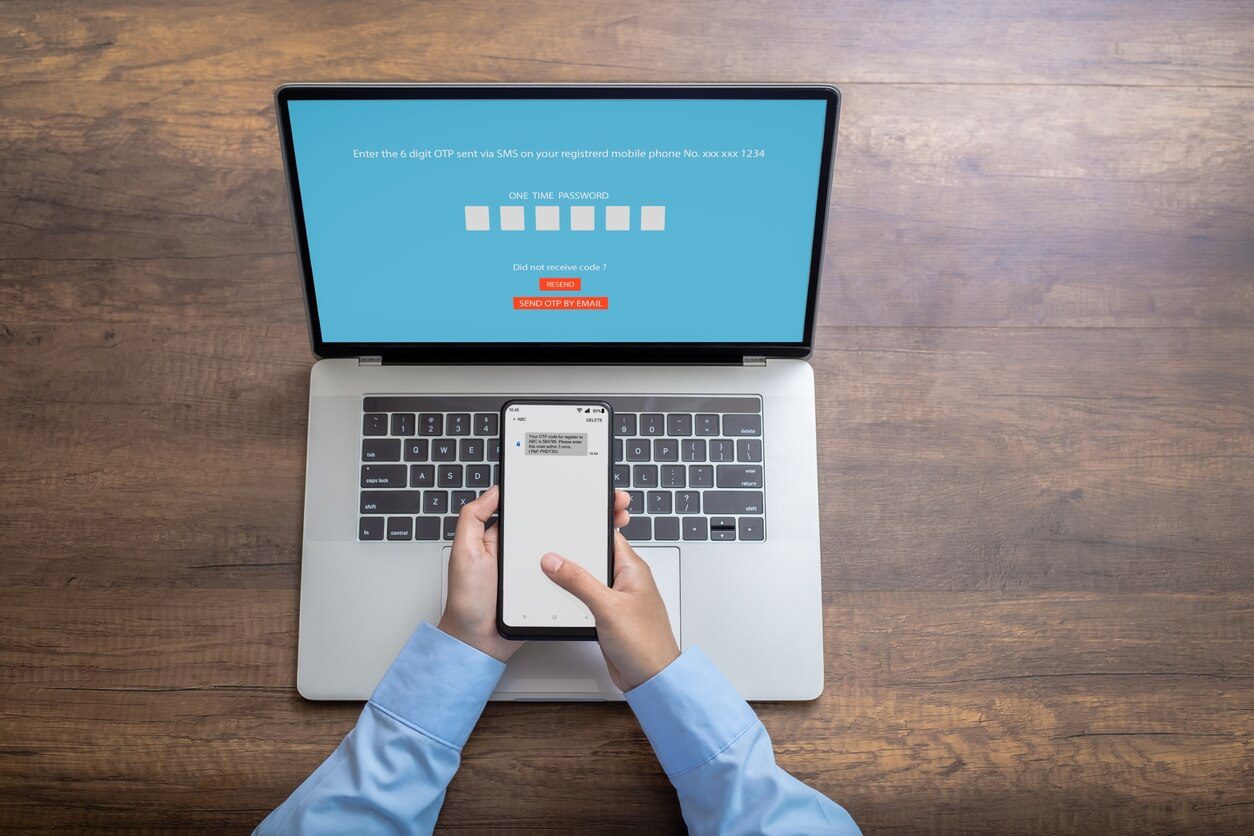
You already know that MFA stands for multi-factor authentication. What does that mean, though? It means you’re setting up multiple sign-in methods to prove you’re the real one accessing your critical systems rather than a hacker.
While MFA can take more time to sign in to your applications, it’s worth the effort to ensure only you or certain employees are gaining access. In the older days, a one-step authentication process could easily be breached.
Hackers, of course, took advantage of this by being able to guess passwords. Data theft also happens internally with one-step authentication. Using more steps makes it more impossible for someone without permission to sign in to any application.
More convenient methods apply to this as Jon points out in our recent YouTube video.
What Common Application Only Needs MFA Occasionally?
As Jon notes, apps like your Office 365 email may only need an MFA every few months. The reason is that when you sign in to Office 365, it usually gives you two tokens: The initial access token, then a refresh token.
Your first token expires after one hour of use. However, the refresh token is often good for two weeks. Continual use of your Office 365 email during this period means you can probably continue an easier sign-in method for up to several months.
It just goes to show MFA differs based on the applications you use the most. Still, you’ll want to set up MFA for other applications in your business.
Jon mentions other types of apps where you should use the MFA system regularly.
Further Apps Needing Multi-Factor Authentication
No doubt your business uses some security programs already. What about the use of a VPN, specifically? VPNs are very popular now in helping to protect networks from hackers. They reroute your IP to other parts of the world so no hacker can trace where you are.
These often need MFA because anyone compromising your VPN could easily tap sensitive data. The whole point of having a VPN is to protect data. It’s why you’re better off using several steps to sign in to one, as inconvenient as it might be.
Another platform that should only be opened with an MFA is any financial server you’re using. These are especially vulnerable due to the sensitive data stored.
Hackers are hungry for things like this, so take time to set up MFA on those items. It also helps to look at the success rate of MFA here in Cincinnati and across the world.
How Successful Is MFA, Really?
According to a report from Microsoft (and reported in Forbes) back in 2019, MFA helps block 99% of all hacking attempts. Hearing this from a company as large as Microsoft should be taken seriously.
One thing they point out is MFA should always be used, no matter how simple your security system is. And, you should use it on more than just Microsoft platforms.
Despite the warnings, not every business adheres to using MFA. Here in Cincinnati, we’ve seen many businesses continually avoid the MFA process, only to find themselves trapped in a scenario of being repeatedly hacked.
Other local organizations often promote MFA. As an example, the University of Cincinnati has a page devoted to two-factor authentication to help their students keep their information safe. Even they would be better off using more than two steps in authentication for the utmost protection.
Setting up Your MFA System
Getting an MFA system set up in your business can sometimes be a challenge without some outside help from IT managed services. The biggest hurdle is moving beyond the use of passwords, something used to sign in to applications for decades.
MFA eliminates having to memorize countless passwords and opens up other paths of user recognition. Eliminating passwords altogether is the better way to go since so many of them are weak. Creating complex ones takes extra time and can cause more confusion.
A good MFA practice is to use at least three types of recognition so it’s impossible for anyone to guess them:
Non-Changing Attributes
Things like fingerprints or face recognition are good examples of an effective MFA system. These are things that never change and help give more personal identification over whom a person really is.
Unique Knowledge
Can you create a question only the user would know? Things like life facts (the name of a favorite pet, etc.) are good ways to make sign-ins extra challenging. Using these makes it easier to remember than a long password.
Using a Certificate or Key
Physical objects are further methods of MFA. Maybe you give each employee specialized certificates or cards they can use as a form of specialized ID.
Where Can You Find Help With MFA?
Take Jon’s comments to heart in our above video. While you may want to get an MFA system underway, it’s often best to let an outsourced IT firm do it for you.
The reason for this is you get an experienced team that knows how to implement it effectively without issues. At 4BIS, we can help you get multi-factor authentication set up for you, including managing your IT security at an optimum level.
Cut through the confusion and let our experienced team be able to handle your security concerns. Cincinnati businesses like yours deserve the very best in a thriving city.
Contact us to learn more about our comprehensive IT services. Keep watching our YouTube videos as we take on individual IT concerns businesses have.
