Rising Global Tensions Mean More Cyber Attacks
Rising Global Conflict Means More Cyber Attacks With conflicts rising in Iran and the Middle East, you might be asking, “How will this affect my…
Why IT Techs Should Want to Work with an Outside Cybersecurity Company
Why IT Techs Should Want to Work with a Cybersecurity Company Let’s get something awkward out of the way- Cybersecurity experts aren’t here to steal…
Edge vs. Chrome: The Browser Battle of 2025
Edge vs. Chrome: The Browser Battle of 2025 Let’s be real: the internet feels like home now. And just like choosing furniture, picking your browser…
Windows 10 Is Retiring – What Businesses Need to Know
Windows 10 Is Retiring – What Businesses Need to Know If your business is still running Windows 10, now’s the time to start thinking about…
Email Security for Businesses: Essential Strategies to Reduce Cyber Threats
Email Security: 11 Ideas to Help Secure My Business Email Safeguarding email communication is vital for every business. Cybercriminals are increasingly sophisticated, and email remains…
Business Email Compromise: What your users need to know
Understanding Business Email Compromise (BEC): How to Spot It and What to Do Business Email Compromise (BEC) is one of the most dangerous threats to…
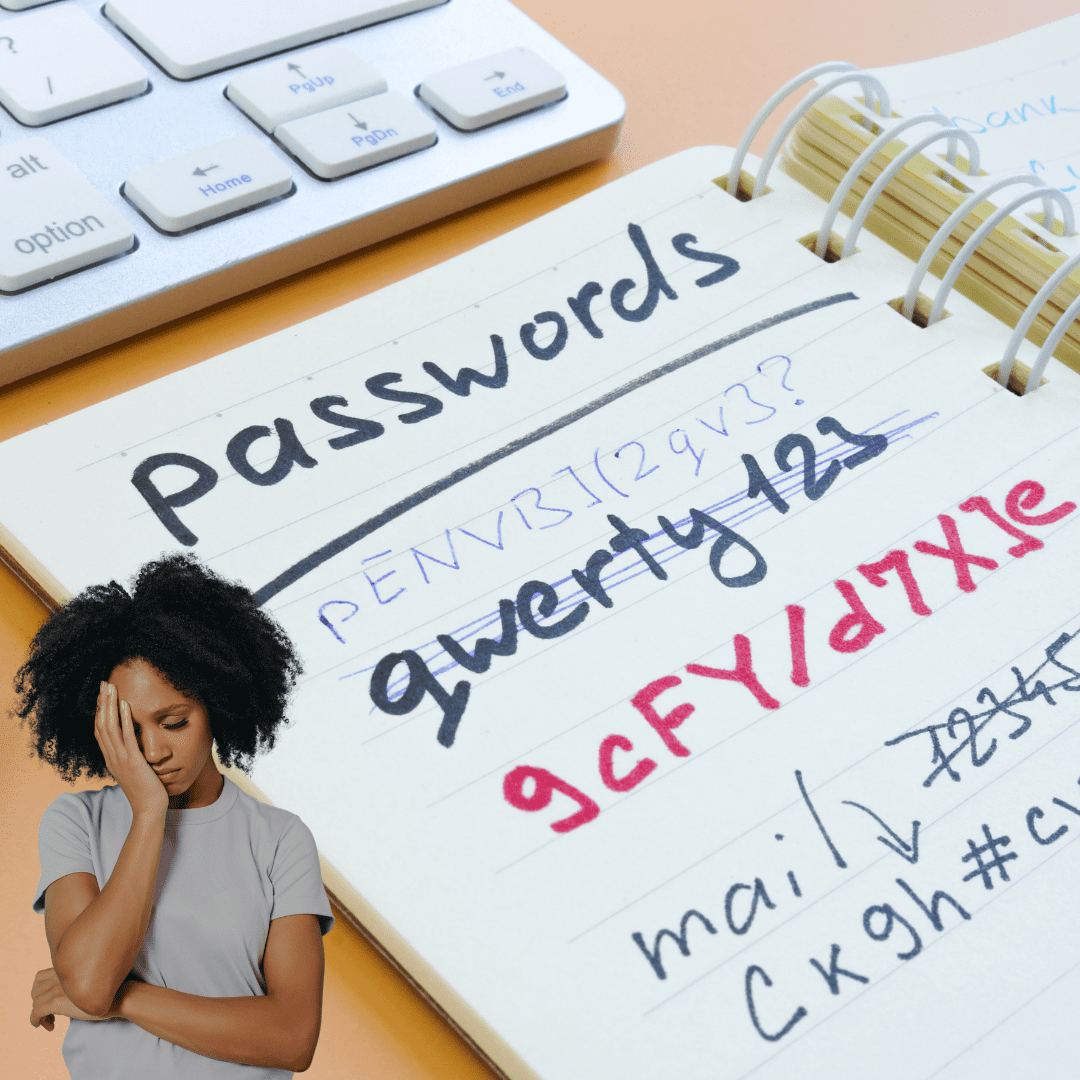
Password Security: A Cyber Security First Approach
The Importance of Password Security: A Cybersecurity First Approach In today’s digital landscape, passwords are the keys that unlock nearly everything we do online. Whether…
A New Era of Secure Remote Access: How SASE Outshines VPNs
SASE: How New Technology Can Help Secure Cincinnati Companies Cyber threats are always evolving. While you are working on your business, hackers are working on…
Passphrase vs Complicated Passwords – Passphrases Are Best
In the world of cybersecurity, the debate around password strength has seen significant evolution in recent years. Traditionally, experts advised creating complex passwords with a…
Personal Data Protection: Tips for Businesses and Consumers
We live in a technology dependent world where we are privileged to have instant communication and access to information readily available. However, these accessibility and…