Rising Global Tensions Mean More Cyber Attacks
Rising Global Conflict Means More Cyber Attacks With conflicts rising in Iran and the Middle East, you might be asking, “How will this affect my…
Why IT Techs Should Want to Work with an Outside Cybersecurity Company
Why IT Techs Should Want to Work with a Cybersecurity Company Let’s get something awkward out of the way- Cybersecurity experts aren’t here to steal…
Edge vs. Chrome: The Browser Battle of 2025
Edge vs. Chrome: The Browser Battle of 2025 Let’s be real: the internet feels like home now. And just like choosing furniture, picking your browser…
Windows 10 Is Retiring – What Businesses Need to Know
Windows 10 Is Retiring – What Businesses Need to Know If your business is still running Windows 10, now’s the time to start thinking about…
Personal Data Protection: Tips for Businesses and Consumers
We live in a technology dependent world where we are privileged to have instant communication and access to information readily available. However, these accessibility and…
Four Ways IT Helpdesk Services Can Enhance Your Daily Operations
Technology is essential to modern daily business operations. However, the complexity of IT systems isn’t always the easiest to understand. Software glitches and hardware malfunctions…
A Quick Guide to The Dos and Don’ts of Seeking IT Help
Software glitches, hardware malfunctions, and other technical issues are inevitable aspects of business operations. Organizations seek to invest in information technology helpdesks to manage them….
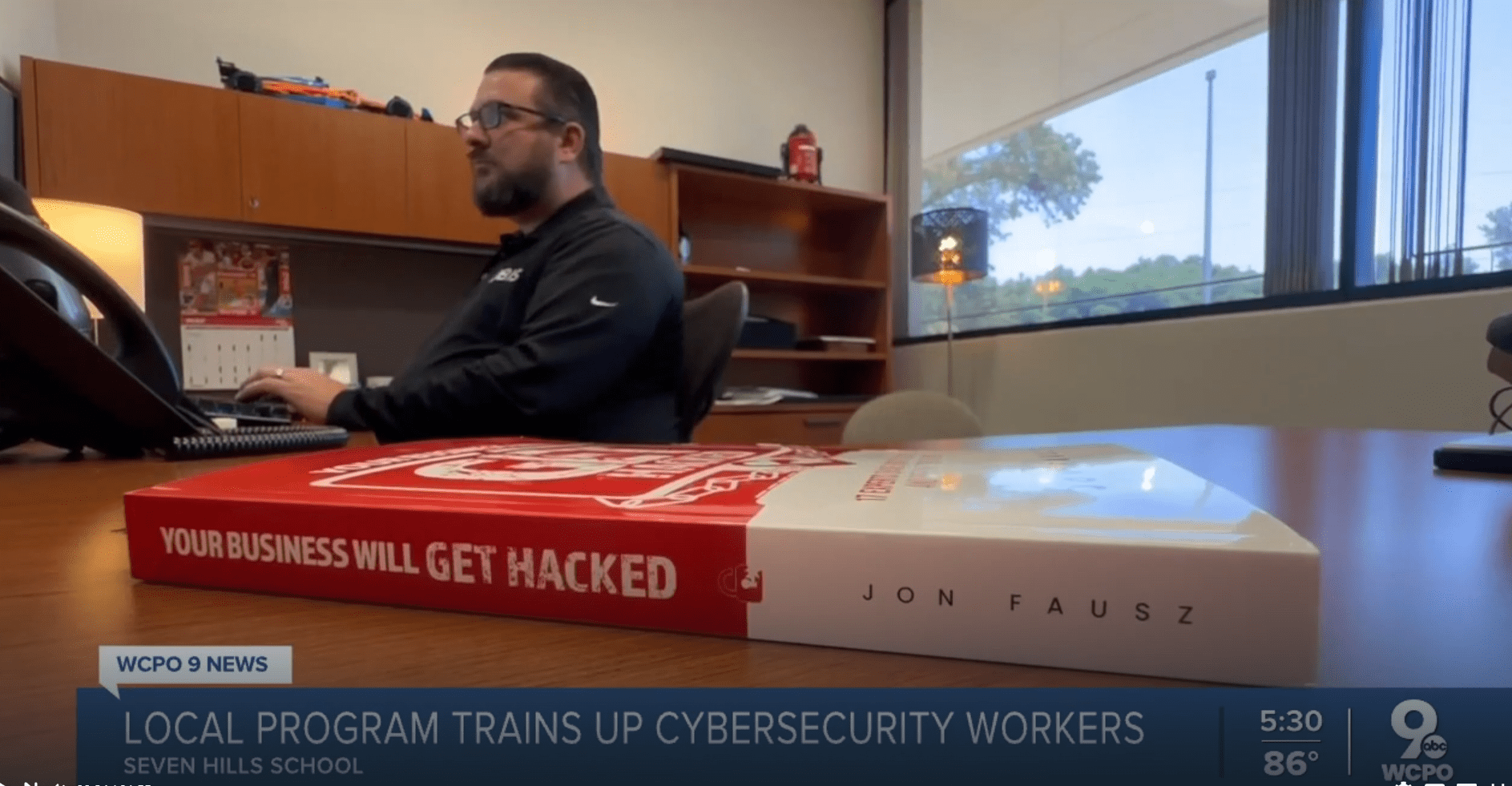
4BIS Featured in News About Cybersecurity Education Program
The Seven Hills School in Cincinnati, Ohio is launching a cybersecurity education program. This program is designed to get high school students interested in pursuing…
Understanding the Importance of Regular IT Audits
Businesses conduct assessments to see what strategies work and what requires tweaking for better performance. One of these assessments is an IT audit—a periodic check-up…
How Social Engineering Tactics Can Put Your Cybersecurity At Risk
Understanding Social Engineering: A Simple Definition Before diving into the complexities of social engineering attacks, it’s crucial to understand what we mean by social engineering….